How to protect your CCTV camera from Hackers (easy steps)
MARCH 10, 2018
It is a proven fact that any device connected to an IP network can suffer attacks and intrusions by hackers and viruses. DVRs and security cameras installed around the world are part of this device list.
You need to protect your devices before they get hacked, and just here in this article you gonna learn how to do it. So just keep reading…
Let’s speak about one of the biggest problems encountered in the area of CCTV, the lack of specialized professionals with IT networks skills .
I have already lost count of how many times I heard the statement below:
“Hey… I understand about IP networks, I know how to configure the DVR with the correct IPs and ports and setup remote viewing to my client, I use a hard to guess password and I change the DVR standard access ports.”
I would like you to understand one basic thing: protection with basic password and different DVR ports is not enough to prevent a hacker from having access to your surveillance system, if a good hacker or virus reaches your DVR, chances are your device will be compromised.
Arrogance is one of the biggest problems
Have you ever heard people saying that they’ve been working with CCTV for many years and have never had problems with a DVR being attacked?
Usually so they are so proud of themselves stating that only inexperienced professionals have problems like this, but not them… it never happened !
But the truth is simple: Such arrogance is based on total guessing, after installing a CCTV system and making it available on the Internet, you are already at risk, no matter if you have changed the password and the device default ports, the device still can be attacked, it’s no 100% safe.
Most DVR installers don’t even have 1% of a hacker skills because those guys have been studying IT network, software development and device intrusion techniques for many years. They know how to get into super-complex systems. So do you really think a DVR or IP camera is protect against such guys ? I don’t think so !

So if you work in the CCTV industry and want to learn how to improve the security of your system, keep reading this article, but keep in mind that you should be humble, so you can always learn and improve your skills.
Related product
What is the operating system of a DVR?
Linux, this is the operating system that is in the majority of the DVRs. They are also in the NVRs and IP cameras. Have you ever used linux before?

This operating system became very popular in the IT industry because it brought the possibility of being used in servers and devices developed by many manufacturers around the world.
It is a system with a central core and several other modules that can be removed to make it leaner. So a DVR or IP camera uses this operating system with all the necessary extra modules tweaked by the manufacturer.
How does a CCTV system work?
Hey, finally you’ll understand a little more about the working mechanism of an IP system, so let’s get started…
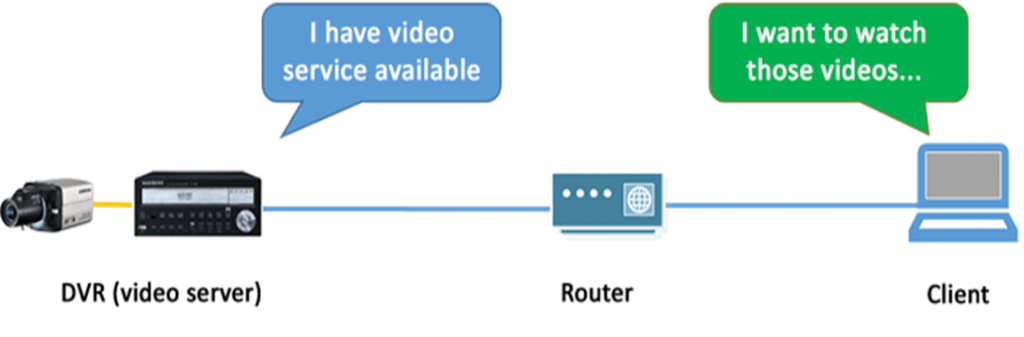
See the diagram below on how IP networks work
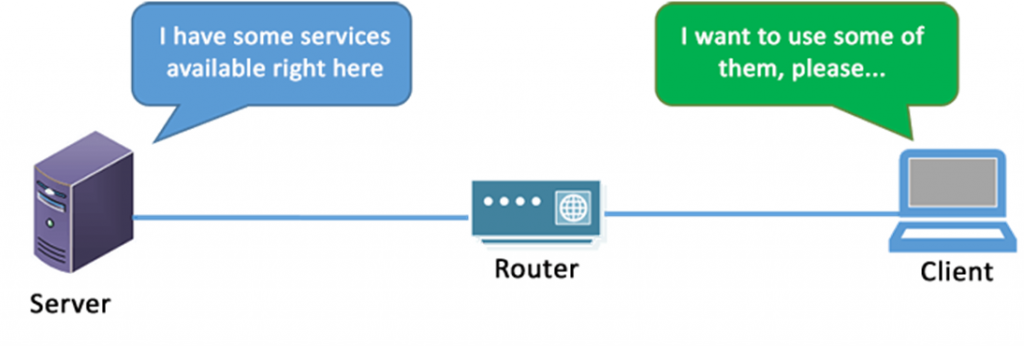
In IP network systems we consider the interaction between devices in a relationship called client-server. There is a server on the network that offers services and clients that use such services.
On CCTV systems, the servers can be DVRs, NVRs, recording servers, IP cameras, encoders, video analysis servers or even access control servers.
Clients are computers, laptops, cell phones, tablets, NVRs. recording servers, access control interface, decoders, etc.
Wait… NVRs and recording servers can be clients too?
Yes, depending on the CCTV system architecture they can be servers that provide videos to computers with monitoring software or they can be clients when they are connecting to an IP camera to request streaming videos to make the recording.
Want to learn more about how CCTV works? read the article: What is CCTV
What are the network vulnerabilities ?
There are many of them, from the simplest attack to the more advanced exploits performed by a hacker (called a cracker when he is an evil attacker).
Possible attacks on a DVR, NVR, or IP Camera:
- Man-in-the-middle password interception
- Brute-force attack (try a sequence of possible passwords)
- Dictionary attack (try a sequence of words like passwords)
- Exploiting vulnerability in services (such as WebServer)
- Denial of service attack (request many concurrent connections)
- Social engineering (getting information through people)
- Network scanning and use of manufacturer default passwords
- intrusion by viruses especially created for these devices
- Former technicians, employees or other people sabotaging the system
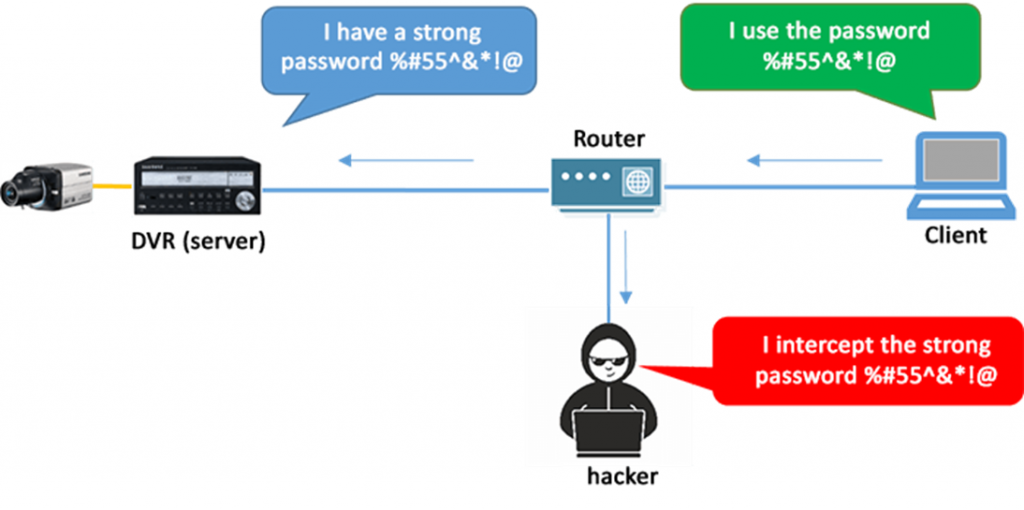
Note below an example of a very common attack used by hackers for many years, called “man-in-the-middle” where the attacker positions himself/herself between the client and server from within the internal network or through the Internet.
By receiving a copy of the password, no matter if it is difficult or not, it may be the longest and most complex password in the universe that it will still be displayed to the hacker’s computer
An attack like this can be avoided by encrypting the password that’s sent between the client and server and also through secure connection via Virtual Private Network.
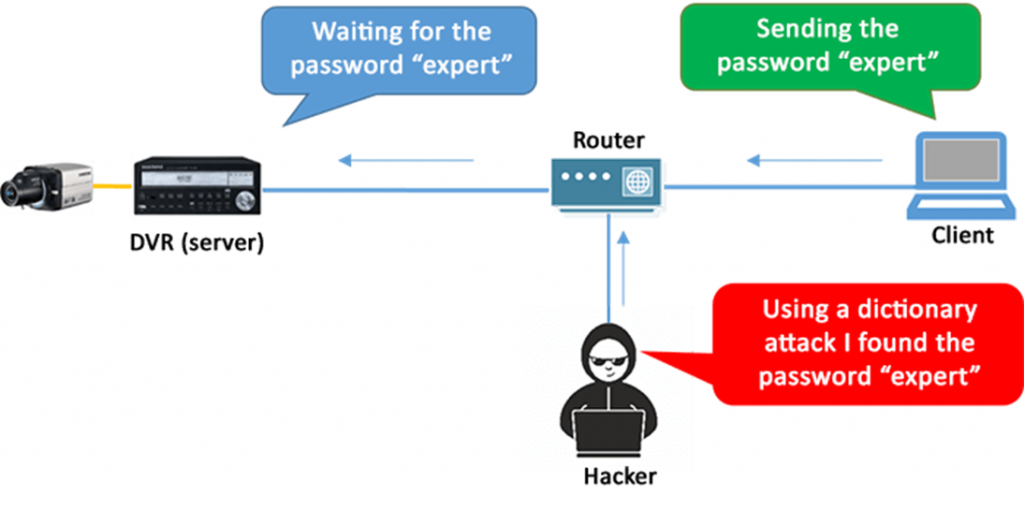
In brute-force attacks and dictionary attacks the hacker uses software to send a fast sequence of passwords to the DVR until it hits the correct one, it’s a trial and error technique pushed really fast by computers.
A software developed for this purpose can try thousands of combinations in a matter of minutes until the computer finds the correct one.
This attack can be prevented with a password policy that combines letters, numbers and special characters, making it really hard to guess.
But again keep in mind that this does not guarantee that your CCTV systemis 100% safe, because in the previously mentioned attack (man-in-the-middle) the attacker can get the password even if it is a hard one.
This is one more step to help protect the system, by combining strong password with encryption or VPN to reduce the risk of successful attacks.
Exploiting device services is also very common among hackers, note that I’m talking about those guys who really know what they’re doing, they are programmers who have software development skills and know how the operating system and services works.
It is possible for a hacker to buy a DVR and study the Linux modules that are available into the CCTV device to find the vulnerabilities and attack it.
This can be avoided with firmware updates created by the manufacturers, the problem lies in the fact that several of them do not pay close attention to this important detail, especially the cheaper’s device manufacturers.

There is also the issue of customers who doesn’t want to pay for a periodic system maintenance which includes device firmware updates.
What happens is that devices are compromised and people don’t even know, because the hacker can simply log into the camera, do whatever he/she wants to and leave the system quietly or even erase all the LOGs with evidence that somebody was logged in the device before.
Even major CCTV manufacturers have such vulnerability issues. For example, the two major Chinese manufacturers have had a so-called “Buffer Overflow” and “RTSP stream authentication”
Security problems like that allow an intruder to have administrator access to NVRs and IP cameras, and despite the fact that the CCTV manufacturer solved the problems, there’s still a lot of equipment installed out there with old firmware and most of them will stay that way forever,

Finally, there is the physical and social engineering issue, because if people who have passwords or direct access to the CCTV systems do not care about security, an attacker can certainly exploit this failure by finding written passwords, or talking to people to find out what they are.
There is no way to implement security to make the CCTV devices 100% safe, but there are ways to reduce the risks and if you don’t have deep knowledge in IT networks, you can at least apply the simplest concepts
Use secure passwords, buy safer and reliable CCTV devices, and make sure the devices have constant firmware updates, maybe you can convince your customer that’s a system maintenance contract it’s a good idea.
A good way to convince your customer about the danger of unprotected CCTV systems is to explain that a strong password policy is not always enough, you can also convince him by showing the site insecam.org where there are thousands of hacked cameras all over the world
Your client’s device may even be on this list or about to get into it.
Go to http://www.insecam.org pick a country and watch the hacked cameras around the world, cross your fingers to not see your device there.
Curlled from: https://learncctv.com/how-to-protect-your-cctv-camera-from-hackers-easy-steps/